Information Security Assessment
Cyber threats evolve every day — and without regular security assessments, your organisation could be exposed and you may not know. An Information Security Assessment gives you a clear, up-to-date view of your vulnerabilities and risks, so you can implement necessary controls and fix weak points before attackers can exploit them.
Our Information Security Assessment dives deep into your IT infrastructure, applications, and processes to uncover hidden risks and security gaps before attackers find them or system failures.
We combine infrastructure analysis, vulnerability analysis and policy reviews to deliver a clear, prioritized action plan. Whether it’s weak points in your network, misconfigured cloud services, or compliance blind spots — we’ll find them.
Benefits of Security Assessments:
- Detect hidden security risks in your network, apps, and cloud
- Be compliant with industry standards and regulations
- Protect sensitive data and customer trust
- Minimize the risk of financial loss
- Minimize downtime
- Strengthen your overall cybersecurity posture
📌 Key Tasks & Activities in an Information Security Assessment
- Define Assessment Objectives and Scope
Identify systems, locations, processes, and data to be assessed. - Collect and Review Existing Security Documentation
Policies, procedures, network diagrams, asset inventories, and access controls. - Conduct IT Asset and Data Inventory Verification
Validate assets, data classification, and ownership. - Perform Threat and Vulnerability Identification
Review known and potential threats affecting systems and data. - Evaluate Security Controls Effectiveness
Assess administrative, physical, and technical controls in place. - Conduct Access Control and Identity Management Review
Verify user access rights, role-based access controls, and account management. - Assess Network Security and Perimeter Defences
Check firewall configurations, IDS/IPS logs, VPN security, and DMZ setups. - Perform Endpoint and Server Security Review
Review antivirus, patching, hardening, and monitoring configurations. - Evaluate Data Protection and Encryption Measures
At rest, in transit, and during processing. - Review Incident Management and Response Capabilities
Incident logs, response plans, and incident handling effectiveness. - Assess Physical Security Controls
Data center, server rooms, and office access security. - Conduct Regulatory and Compliance Requirements Check
Mapping to standards like ISO 27001, NESA, HIPAA, PCI DSS, etc. - Perform Risk Assessment and Identify High-Risk Areas
Risk likelihood, impact analysis, and mitigation recommendations. - Document Findings, Gaps, and Areas for Improvement
Detail all weaknesses and non-conformities. - Develop a Final Security Assessment Report
Include risk ratings, recommendations, and an executive summary.
📦 Deliverables of an Information Security Assessment
- Assessment Scope & Methodology Document
Outlining what was reviewed, how, and against which standards or frameworks. - Asset and Data Inventory Report
Verified list of IT assets, data types, classifications, and ownership. - Threat and Vulnerability Register
Documentation of identified risks and potential vulnerabilities. - Security Controls Evaluation Report
Findings on the effectiveness and gaps in technical, administrative, and physical controls. - Access Control and Identity Management Review Report
List of access rights, privilege escalations, and access management weaknesses. - Network Security Assessment Summary
Firewall rules review, perimeter defence analysis, and external exposure findings. - Endpoint and Server Security Review Report
Antivirus, patch management, and system hardening assessment results. - Data Protection and Encryption Practices Review
Assessment of data security at rest, in transit, and processing controls. - Incident Management Assessment Report
Findings on incident logging, response readiness, and process effectiveness. - Compliance Requirements Mapping Report
Alignment status against ISO 27001, NESA, PCI DSS, HIPAA, etc. - Physical Security Review Summary
Site security controls, access logs, and surveillance review results. - Risk Assessment Report
Including a risk register, likelihood and impact ratings, and prioritized risks. - Recommendations and Remediation Roadmap
Actionable steps for addressing identified gaps and improving controls. - Executive Summary Presentation
High-level overview of findings, key risks, and recommendations for leadership. - Final Information Security Assessment Report
Consolidated report containing all assessments, findings, risks, and recommendations.

Key Features of Our Assessments
Survey and Data Gathering
Consultants will examine all the components in the IT infrastructure and acquire data by:
– Physical survey of data centres, computer rooms
– Interviews with IT staff
– Inspection of systems, configurations, documentation
Documentation
Work products in this phase include:
– Documentation of servers, networks, applications, services, etc.
– Topology and connectivity diagrams
– Server and equipment lists
Assessment & Analysis
Adequacy of controls will be tested against
– Controls based on standards/frameworks:
– ISO27001/PCI-DSS/NIST etc
– Test controls in all security domains
– Technology assessment by VA tools
Quality Reports
Summary reports and detailed reports will be submitted. The granularity of reports and types of reports vary according to the scope and requirements of the client.
Recommendations
Based on the business requirements:
– Highlighting areas requiring immediate action
– Configuration changes or system upgrades
– Implementation of new controls
Presentation & Workshop
– Presentation of findings: Executive Summary
– Discussing recommendations with the team
– Workshop with tech and admin teams

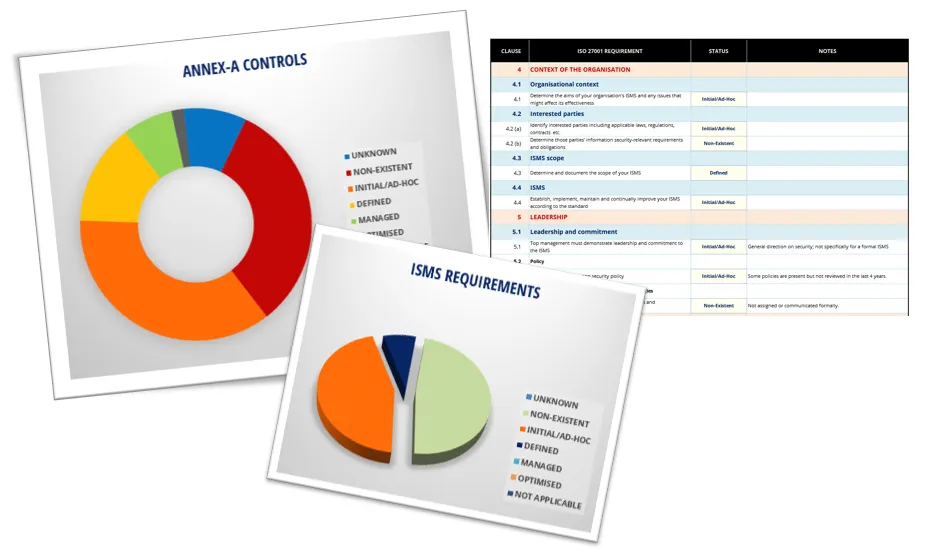
Sample Deliverables
Assessment Report
Detailed reports, Summary reports and Executive Summaries on the state of security and status of implemented controls.
Gap Analysis Report
Gap Analysis against established standards and frameworks such as ISO27001 or NIST.
Documentation
Asset inventory: servers, storage, backup, network equipment, cloud assets.
Diagrams
Network connectivity and topology diagrams, traffic flow, infrastructure architecture, server architecture diagram, etc.






